So one evening recently I got an email alert for a big spike in traffic going to this blog. I don’t know why it happened and I don’t see my post view counts getting that high either so it was a strange event. Thankfully Cloudflare’s service was able to handle the total requests being made as I don’t have much visibility on the WordPress side of things. My blog setup here is a bit simplified unfortunately!
Security Camera Tech – A Crime Was Committed Against Me!
Well, my grandpa had a saying that I remember til this day, he said “son, nothing good ever happens at 4am”. So last night, at 4:15am, 2 folks stole my license plate off my car and they could be out there committing crimes in my name!
A History Of Console Gaming
So I usually try to save my money where possible and I don’t celebrate my birthday but I wanted get an updated gaming console so that I could continue to play Fortnite when I have some free down time. Way back in the day, my grandpa gave me an original Nintendo (which I sadly didn’t think of keeping over time) and eventually I got the Nintendo 64 when it came out as well. I then purchased the original Xbox (which had the Halo title on it) and that was one of my first Microsoft products that I enjoyed owning. After that, I switched over to the Sony side and purchased the Playstation 2 – and then the Playstation 3 – and then the Playstation 4 (so that I could keep playing the different GTA versions).
For my birthday this Jan 2023, after spending years playing with the original PS4, it was getting a little old and hot and dusty so I purchased myself a gift of the Playstation 5 (to be able to play the Fortnite battle royals). However, once I turned it on, configured it, updated it, downloaded the game and launched it – the entire system powered off. I tried it again and the same thing happened at the same spot in the game. I also tried to download a free title that came with the system and it also shut off, right before the game play starts. I recorded a long boring video of it because I couldn’t believe it!
This new unit left me in such disbelief that I went back to Microsoft and purchased an Xbox Series X instead! I have to say that as a long time Playstation fan, I was pretty impressed with the build quality of this gaming console. It has a good weight to it, it’s less bulky, has proper ventilation holes near the back bottom for cool air and the main fan near the top has nice big blades which quietly moves the air upwards and outwards – it’s properly engineered and designed – it reminds me of a little chimney stack! My only improvement would be if they could just round out the corners with a small radius to make them a little more user friendly and less sharp feeling/looking 🙂
The PS5 is fairly big and bulky, the fan blades are way too small sized and it doesn’t really have proper ventilation holes or airflow direction – and according to my online searches, other people have also been facing power / heat issues with it. The only downside to the Xbox is that I highly prefer the PS5 controller over it as the bumper/trigger buttons are less bulky, the joy-sticks are symmetrically aligned, the D-Pad is in the proper location and the overall feeling/comfort is much nicer while holding it. I was even able to buy a little add-on attachment for the Xbox that allows me to still continue to use the PS5 controller which is amazing!
The ultimate gaming console setup for me in 2023 is the: Microsoft Xbox Series X ++ Sony Playstation 5 Controller
Last keyboard mod before the end of the year!
Update: fossjon/the-tale-of-the-three-tactiles
Well, this year has been a long and crazy one for me and I wanted to upgrade the style of my first mechanical keyboard. Even though it’s not my fav one to type on, it is still a memorable part of my collection and it’s a great WFH keeb. I bought a wood case which raises it up a little but it’s much more solid, better sounding and nicer styling compared to the cheaper, thinner, and hollow plastic case that comes with ducky keyboards!
First keyboard build for the year end!
Update: fossjon/keyboard-gear-update-the-five-tactiles
This was my first mechanical keyboard build and they have made it a pretty smooth process (took me half a day to lube the stabs). This is the KBD67 ANSI hot-swap and I put in a mixture of everything into it. It has holy panda switches for the alphas, halo true switches for all else, and ducky plus drop keycaps. It has a pretty good typing feeling, feedback, and sound to it – it’s a little lower in pitch compared to the Drop Alt’s open top metal frame (I think the plastic and padding underneath help deepen the sound). It’s a great overall keyboard to have as part of the collection! 🙂
~
Related:
Firewall Redirect Connection State Hook Mod for NGINX Stream Proxy Server
So nginx has a stream proxy module that you can use for transparent SSL/TLS relaying/forwarding, however, it is only capable of reading the SNI hostname upon the initial handshake of the connection. In addition, the destination IP address is replaced because of the firewall redirect pointing to the proxy server. I wrote a small modification that can be compiled into nginx which allows you to run a script that can pull the missing destination IP address from a given state connection table in a firewall, for example pfctl or iptables.
Source: https://github.com/stoops/nginx
Reproduction Test:
echo 'test' | nc 8.8.4.4 443
Error Log:
[error]: no host in upstream ":443", client: 192.168.X.Y, server: 0.0.0.0:3129, …
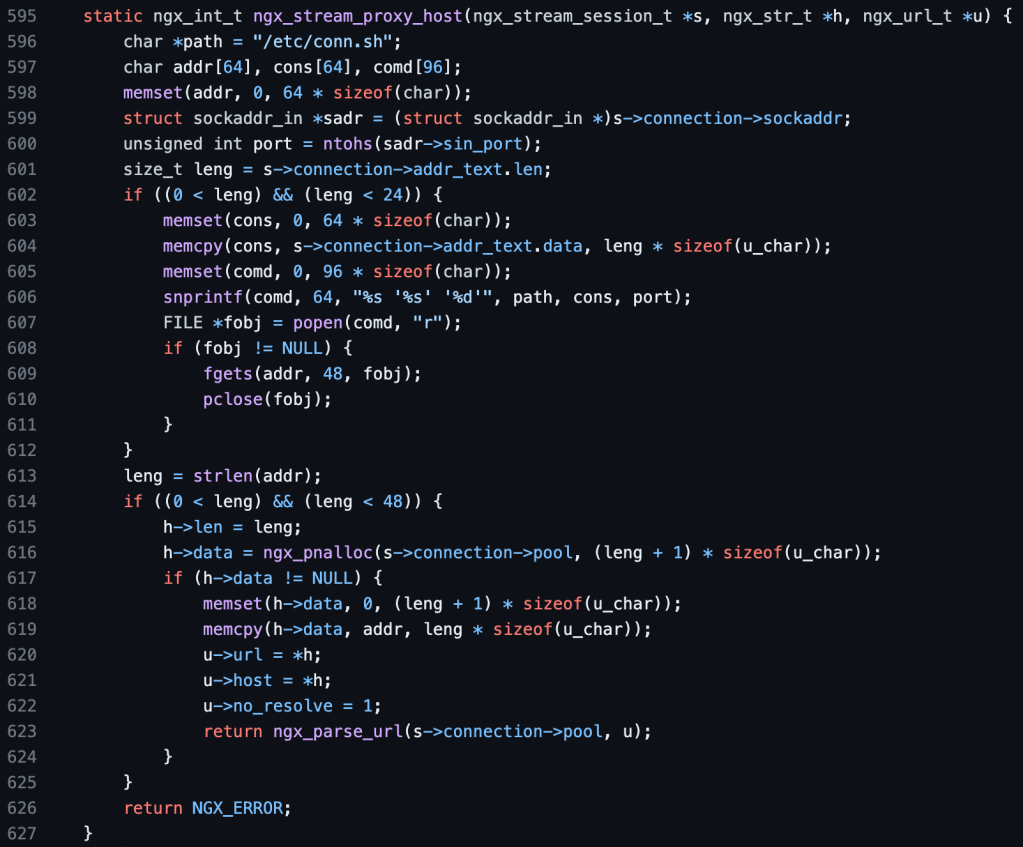
C Hook Mod:
This code mod above will allow you to run a shell script of your choosing if nginx cannot get the hostname or address of a connection requesting to be proxied. You can then look up the destination IP address based on source IP + port combo from the connection state mapping table of the firewall. The result is a much more stable proxying experience for HTTPS connections without needing to wait for the SNI or hostname of the initial handshake!
Bonus: This mod also allows you to use nginx as a generic UDP proxy forwarder/server for the first time with the following configs below for the various connection states. This can be used for proxying protocols such as DNS and QUIC and some other VPN related ones. Note, you may need to adjust your own individual timeout values to match your needs.
VPN+MTU:
user root wheel;
worker_processes 1;
worker_rlimit_nofile 8192;
events {
accept_mutex off;
multi_accept off;
worker_connections 1024;
#use select;
}
stream {
resolver 1.1.1.1 ipv6=off;
server {
listen 127.0.0.1:3121 udp;
proxy_half_close off;
proxy_socket_keepalive off;
proxy_connect_timeout 30s;
proxy_timeout 45s;
proxy_pass $proxy_protocol_server_addr:1;
}
}rdr on en0 inet proto udp from any to any port 4500 -> 127.0.0.1 port 3121
DNS:
user root wheel;
worker_processes 1;
worker_rlimit_nofile 8192;
events {
accept_mutex off;
multi_accept off;
worker_connections 1024;
#use select;
}
stream {
resolver 1.1.1.1 ipv6=off;
server {
listen 127.0.0.1:3125 udp;
proxy_half_close off;
proxy_socket_keepalive off;
proxy_connect_timeout 15s;
proxy_timeout 5s;
proxy_pass $proxy_protocol_server_addr:1;
}
}rdr on en0 inet proto udp from any to any port 53 -> 127.0.0.1 port 3125
QUIC:
user root wheel;
worker_processes 1;
worker_rlimit_nofile 8192;
events {
accept_mutex off;
multi_accept off;
worker_connections 1024;
#use select;
}
stream {
resolver 1.1.1.1 ipv6=off;
server {
listen 127.0.0.1:3123 udp;
proxy_half_close off;
proxy_socket_keepalive off;
proxy_connect_timeout 15s;
proxy_timeout 5s;
proxy_pass $proxy_protocol_server_addr:1;
}
}rdr on en0 inet proto udp from any to any port 443 -> 127.0.0.1 port 3123
Update: Alternative Load Balancing With Single-Process NGINX
~
The Tale Of The Three Tactiles
Update: fossjon/first-keyboard-build-for-the-year-end
So I was a little late to the game on mechanical keyboards but I tried my best to catch up in 2022 and so I could try to make it into 2023. The first one I got was the Ducky-Mini with Cherry MX Brown switches which offers a bit of a quieter/smoother version of a tactile switch or a rougher/scratchier version of a linear. This is a good wfh keyboard as it’s not as annoying to type on while in the middle of meetings and it offers more feeling during key travel compared to a linear in addition to lesser sound compared to a clicky. I then picked up a Drop-Alt and put Holy Panda switches in it and the feeling and sound matched more closely to the tactile experience which other reviewers were talking about. It’s a solid and stable keyboard and the key press feedback feeling and sound reminds me more of an olden analogue type writer. It’s a much more enjoyable keyboard to type on — a true tactile experience. I lastly purchased a Matias-Mini with Alps White switches that are both clicky and tactile. This is a fun keyboard to type on for personal projects as it has the same characteristics of the Drop keyboard but with a slightly louder and higher pitched sound to it. It’s a great keyboard for all Mac enthusiasts!
BSD PF firewall has one extra scrub option…
The BSD PacketFilter firewall has an extra scrub option which is, “reassemble tcp”. I was researching and exploring the different types of fragmented-packets/segmented-streams of data that could be forwarded within a network that may have a smaller MTU link in the middle of the routing path. I am still reading about what this option does on a streamed session and if Linux has anything similar to it…
Note: nftables has user-land hooks via nfqueue
# nft insert rule ip mangle FORWARD ip daddr 8.8.4.4 tcp dport 53 counter queue num 1
from scapy.layers.inet import IP
from netfilterqueue import NetfilterQueue
def que_packet(pkt):
pay = pkt.get_payload()
ipf = IP(pay)
print("pkt",pkt)
ipf.show()
pkt.accept()
nfqueue = NetfilterQueue()
nfqueue.bind(1, que_packet)
try:
nfqueue.run()
except:
print("exit")
nfqueue.unbind()
Edit: I found that it was a bit complicated trying to understand when optimized network stacks (software or hardware) will combine multiple TCP segments into bigger IP packet payloads and that trying to perform reassembly at that higher level was a bit challenging/difficult. I came up with a way to solve the occasional web site having slow upload speeds for large files by running an nginx transparent reverse proxy server for HTTP/HTTPS instead!
HTTPS:
user root wheel;
worker_processes 1;
worker_rlimit_nofile 8192;
events {
accept_mutex off;
multi_accept off;
worker_connections 1024;
#use select;
}
stream {
resolver 1.1.1.1 ipv6=off;
server {
listen 127.0.0.1:3129;
ssl_preread on;
proxy_half_close off;
proxy_socket_keepalive off;
proxy_connect_timeout 45s;
proxy_timeout 90s;
proxy_pass $ssl_preread_server_name:443;
}
}rdr on en0 inet proto tcp from any to any port 443 -> 127.0.0.1 port 3129Update: Modifying the nginx framework to proxy more generically/reliably
~
More Nostalgia The Older I Get
Well, 2022 was a long and crazy year for me (health wise as well) but I’m trying to get back on track and focus and concentrate on new things in life! I’ve been finding that the older I get, the more I think about the olden golden days of being a kid and growing up in an analogue world, before the invention of the internet and computers. Times were simpler but more basic and it’s kinda crazy to think about how much progress and change exists nowadays. I remember a time when my specific search term in Google actually showed me the exact thing I was looking for haha 🙂 Anyway, I’ll try to keep this blog going as a personal hobby of interesting things that I find out along the way in life. Just random tech craziness if you will!
~
Implementing pf-scrub no-df bit in a Netfilter Linux Kernel Module hook – IPV4 Packet Header Rewrite
So, I was searching around for the Linux equivalent of the BSD PF firewall rule “scrub-all no-df” and I was expecting that there would be an “iptables mangle prerouting” version – but – no luck! I just wanted to be able to clear this specific bit in the IPv4 packet header with a Linux router so that it would be able to fragment the packets along the inner routes that may have a lower MTU set. Since I couldn’t find anything I made one myself 🙂
Source: https://github.com/stoops/nf_df
Code Snippet

Test Command
ping -c 1 -M do -s 123 1.1.1.1Packet Capture
As you can see below, the first IPv4 packet (unmodified) contains the DF bit flag set on (0x0000: …. 4000 ….) compared to the modified packet below in the “After Send” section.
Before Send
21:58:39.473143 fe:00:00:00:01:02 > fe:00:00:00:01:01, ethertype IPv4 (0x0800),
length 165: 1.3.3.7 > 1.1.1.1: ICMP echo request, id 19298, seq 1, length 131
0x0000: 4500 0097 0000 4000 4001 6348 0103 0307 E.....@.@.cH....
0x0010: 0101 0101 0800 6735 4b62 0001 0f74 6d63 ......g5Kb...tmc
0x0020: 0000 0000 2538 0700 0000 0000 1011 1213 ....%8..........
0x0030: 1415 1617 1819 1a1b 1c1d 1e1f 2021 2223 .............!"#
0x0040: 2425 2627 2829 2a2b 2c2d 2e2f 3031 3233 $%&'()*+,-./0123
0x0050: 3435 3637 3839 3a3b 3c3d 3e3f 4041 4243 456789:;<=>?@ABC
0x0060: 4445 4647 4849 4a4b 4c4d 4e4f 5051 5253 DEFGHIJKLMNOPQRS
0x0070: 5455 5657 5859 5a5b 5c5d 5e5f 6061 6263 TUVWXYZ[\]^_`abc
0x0080: 6465 6667 6869 6a6b 6c6d 6e6f 7071 7273 defghijklmnopqrs
0x0090: 7475 7677 7879 7a tuvwxyz
Before Recv
21:58:39.475300 fe:00:00:00:01:01 > fe:00:00:00:01:02, ethertype IPv4 (0x0800),
length 165: 1.1.1.1 > 1.3.3.7: ICMP echo reply, id 19298, seq 1, length 131
0x0000: 4500 0097 d279 0000 3901 d7ce 0101 0101 E....y..9.......
0x0010: 0103 0307 0000 6f35 4b62 0001 0f74 6d63 ......o5Kb...tmc
0x0020: 0000 0000 2538 0700 0000 0000 1011 1213 ....%8..........
0x0030: 1415 1617 1819 1a1b 1c1d 1e1f 2021 2223 .............!"#
0x0040: 2425 2627 2829 2a2b 2c2d 2e2f 3031 3233 $%&'()*+,-./0123
0x0050: 3435 3637 3839 3a3b 3c3d 3e3f 4041 4243 456789:;<=>?@ABC
0x0060: 4445 4647 4849 4a4b 4c4d 4e4f 5051 5253 DEFGHIJKLMNOPQRS
0x0070: 5455 5657 5859 5a5b 5c5d 5e5f 6061 6263 TUVWXYZ[\]^_`abc
0x0080: 6465 6667 6869 6a6b 6c6d 6e6f 7071 7273 defghijklmnopqrs
0x0090: 7475 7677 7879 7a tuvwxyz
Kernel Module
# lsmod | grep -i nf_df
nf_df 16384 0After Send
21:52:52.646803 fe:00:00:00:01:02 > fe:00:00:00:01:01, ethertype IPv4 (0x0800),
length 165: 1.3.3.7 > 1.1.1.1: ICMP echo request, id 52199, seq 1, length 131
0x0000: 4500 0097 0000 0000 4001 a348 0103 0307 E.......@..H....
0x0010: 0101 0101 0800 0e11 cbe7 0001 b472 6d63 .............rmc
0x0020: 0000 0000 56d8 0900 0000 0000 1011 1213 ....V...........
0x0030: 1415 1617 1819 1a1b 1c1d 1e1f 2021 2223 .............!"#
0x0040: 2425 2627 2829 2a2b 2c2d 2e2f 3031 3233 $%&'()*+,-./0123
0x0050: 3435 3637 3839 3a3b 3c3d 3e3f 4041 4243 456789:;<=>?@ABC
0x0060: 4445 4647 4849 4a4b 4c4d 4e4f 5051 5253 DEFGHIJKLMNOPQRS
0x0070: 5455 5657 5859 5a5b 5c5d 5e5f 6061 6263 TUVWXYZ[\]^_`abc
0x0080: 6465 6667 6869 6a6b 6c6d 6e6f 7071 7273 defghijklmnopqrs
0x0090: 7475 7677 7879 7a tuvwxyz
After Recv
21:52:52.669611 fe:00:00:00:01:01 > fe:00:00:00:01:02, ethertype IPv4 (0x0800),
length 165: 1.1.1.1 > 1.3.3.7: ICMP echo reply, id 52199, seq 1, length 131
0x0000: 4500 0097 79f9 0000 3901 304f 0101 0101 E...y...9.0O....
0x0010: 0103 0307 0000 1611 cbe7 0001 b472 6d63 .............rmc
0x0020: 0000 0000 56d8 0900 0000 0000 1011 1213 ....V...........
0x0030: 1415 1617 1819 1a1b 1c1d 1e1f 2021 2223 .............!"#
0x0040: 2425 2627 2829 2a2b 2c2d 2e2f 3031 3233 $%&'()*+,-./0123
0x0050: 3435 3637 3839 3a3b 3c3d 3e3f 4041 4243 456789:;<=>?@ABC
0x0060: 4445 4647 4849 4a4b 4c4d 4e4f 5051 5253 DEFGHIJKLMNOPQRS
0x0070: 5455 5657 5859 5a5b 5c5d 5e5f 6061 6263 TUVWXYZ[\]^_`abc
0x0080: 6465 6667 6869 6a6b 6c6d 6e6f 7071 7273 defghijklmnopqrs
0x0090: 7475 7677 7879 7a tuvwxyz
Edit: In addition to this Linux kernel nftables module, I found out that there is another one running for IPv4 packet defragmentation which should also be similar to the scrub rule “fragment reassemble”. According to the documentation, if you have any stateful connection tracking rules for layer-4 (for example, postrouting nat rules or prerouting udp ports) then the fragmented packets should get reassembled again. I am looking into the scrub rule “reassemble tcp“…
# lsmod | grep -i defrag
nf_defrag_ipv4 16384 1 nf_conntrack
~
Experiment: Tunnelling my WAN over VPN
So I had this Mac Mini that I was originally using as a WiFi relay bridge (layer 2) but since then I was only using it as an rsync backup server. I decided to also turn it into a VPN tunnelling router (layer 3) for my home network setup by using OpenVPN on MacOS (connected to a Debian Linux server). I was testing out its performance and it was holding up pretty good and stable but I wanted to give WireGuard a try as well, just to see and compare. Upon initial configuration, I noticed that WireGuard was defaulting to a lower MTU (1420) compared to what I had set in OpenVPN (1450) and that some of my connections to websites were unstable/slow/hanging. Additionally, with OpenVPN, I was able to set some extra settings like MSS & fragmentation limits and I couldn’t find the equivalent of those with WireGuard. However, I do like the overall simplicity of the WG config and setup process!
I actually lowered the WG MTU (1410) but this could potentially cause larger size packets to fragment. I was searching around and found that it was possible for one to clamp the MSS values on forwarded/routed packets with an iptables forward/mangle rule. Since the Mac is the VPN client and has the BSD PF firewall, I also set a scrub rule as well:
# bsd pf
scrub all no-df random-id max-mss 1330
# nix nf
iptables -t mangle -A POSTROUTING -p tcp --tcp-flags SYN,RST SYN -j TCPMSS --set-mss 1330
# iptables-translate ftw!
I was also trying to read more about the “don’t fragment” bit that could get set on packets along the way (sometimes when the PMTUD setting is enabled) and the pf-scrub rule can help to clear that bit (no-df) where I couldn’t yet find the equivalent on the Linux side. I also tried setting these sysctl values as well:
# mac
sysctl net.inet.tcp.path_mtu_discovery=0
# nix
sysctl net.ipv4.ip_no_pmtu_disc=1
I’m still playing around with this setup but it’s been an interesting networking experiment so far in terms of seeing how your web connections handle and react to being encapsulated automatically by a network router…
Edit: I have written a Linux kernel module to do the equivalent of “scrub-all no-df“
Tunnelled Internet – 1G WAN – Speed Test

~
A place to finally put all of my stuff!
Well it’s been a tough number of years for me as all of my personal belongings have been packed up in boxes the entire time, however, I have finally been able to move into a new space and a new place.
As a new decorative piece to hang on the wall, I was able to get a large size, glass print of the MacOS flying Apple desktop background wallpaper I created from Fracture Me. It helps to add a little more fun and colour inside and they have pretty good quality printers (quick service as well).
This will be a new journey for me!




~
OpenWRT Switches From iptables To nftables!
So after many years of using and learning iptables, one of my favourite firewalls, I had to translate my command line ruleset into a new format/syntax. It wasn’t too bad but with the added power and flexibility of nftables, it can be harder to find the order/priority of the rules for a given filter hook, for example, INPUT. However, I really appreciate how the new firewall incorporates some previous features that I used to have to install via iptables modules like ipset and hashlimit, which provides the rate limiting functionality!
hook="input"
nft list ruleset \
| sed -e 's/counter.*[0-9]//g' \
| tr '\t' ' ' | tr '\r\n' '~' | tr '{}' '\n' \
| grep -i "hook.${hook}" \
| tr '~' '\n' \
| grep -i '[a-z]' \
| sed -e 's/^[ ]*//'
type filter hook input priority filter; policy accept;
iifname "lo" accept
iifname "lan" udp dport 67 accept
iifname "wan" ct state established,related accept
dropHacky – Restart Network Interface On OpenWRT
So on OpenWRT for example, a WAN interface can be set get an IP address via DHCP, however, this will launch a separate independent process on Linux to act as the client. On the web interface, there is a button on each network interface which allows you to restart that individual interface (and in addition, it will be smart enough to kill the previous client process and launch a new one as well as re-initialize the firewall and other stuff). I could not find the equivalent command line option to this as a simple ifdown/sleep/ifup would not capture all of these sub-actions as per the extra configurations set on the interface. So I searched and read a helpful hint that can give a similar workaround using the network init startup script. You can modify some small part of the network interface configuration and then call network reload which will be smart enough to pick up the diff/changes only. This helps greatly in case you need to script or schedule a specific interface restart:
#!/bin/sh
r=$(/bin/date | /usr/bin/md5sum | /usr/bin/cut -c 1-8)
/sbin/uci set network.wan.hostname="owrt${r}"
/sbin/uci commit network
/etc/init.d/network reloadLocal HTTP Proxy Server – Bypass Host Regex Match – Multi Destination Client Connection
No usage documentation, however, posting this for historical purposes:
#ok:www.google.com:false python3 proxy.py ~/.proxy.txt host:port export https_proxy='http://127.0.0.1:9090'
import os, sys, re
import select, socket, socketserver
class proxysrv(socketserver.BaseRequestHandler):
def init(self):
self.size = (8 * 1024)
self.file = sys.argv[1]
self.info = sys.argv[2].split(":")
self.host = (self.info[0], int(self.info[1]), True)
self.sock = self.request
def config(self, file):
proxlist = []
try:
fobj = open(file, "r")
for line in fobj.readlines():
line = line.strip().split(":")
stat = False
if ("true" in line[2].lower()):
stat = True
proxlist.append([line[0], line[1], stat])
except:
print("error","config")
return proxlist
def checks(self, conf, data):
try:
proxyreq = data.decode().split("\n")
hostreqs = proxyreq[0].strip().split(" ")
hostinfo = hostreqs[1].split(":")
hostname = hostinfo[0]
hostport = int(hostinfo[1])
lasthost = ()
for item in conf:
regx = re.match("^.*%s$" % (item[1]), hostname)
if ((item[0] == "no") and (not regx)):
lasthost = (hostname, hostport, item[2])
if ((item[0] == "ok") and regx):
lasthost = (hostname, hostport, item[2])
if (lasthost and (not lasthost[2])):
return lasthost
except:
print("error","checks")
return self.host
def newcon(self, srcs, data, host):
try:
senddata = "HTTP/1.1 200 Connection established\r\nProxy-Connection: Keep-Alive\r\n\r\n".encode()
sockobjc = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sockobjc.connect((host[0], host[1]))
if (host[2]):
sockobjc.sendall(data)
else:
srcs.sendall(senddata)
return sockobjc
except:
print("error","newcon")
return None
def relays(self, srcs, dsts):
try:
while True:
(readlist, _, _) = select.select([srcs, dsts], [], [])
for sockitem in readlist:
if (sockitem == dsts):
data = dsts.recv(self.size)
print("dsts",len(data))
if (not data):
raise
srcs.sendall(data)
if (sockitem == srcs):
data = srcs.recv(self.size)
print("srcs",len(data))
if (not data):
raise
dsts.sendall(data)
except:
pass
def handle(self):
self.init()
proxlist = self.config(self.file)
recvdata = self.sock.recv(self.size)
desthost = self.checks(proxlist, recvdata)
sockobjc = self.newcon(self.sock, recvdata, desthost)
print("addr",self.client_address)
print("data",recvdata)
print("host",desthost)
if (sockobjc):
self.relays(self.sock, sockobjc)
if (__name__ == "__main__"):
for e in ["http_proxy", "https_proxy", "no_proxy"]:
for v in [e.upper(), e.lower()]:
print("envr",v)
os.environ[v] = ""
sockobjc = socketserver.TCPServer(("127.0.0.1", 9090), proxysrv)
sockobjc.serve_forever()